Help with Supabase Trigger: Permission Denied for Anon Role on auth.users Table
Hello,
I'm new to Supabase and SQL, and while I'm slowly getting the hang of it, I've been stuck on this issue for days and could really use some help.
What I'm Trying to Solve
I’m building an iOS app and creating a login system. I want to take newly inserted information from the auth.users table (specifically, ID, email, and password) and copy it into a table in the public schema (p_users).
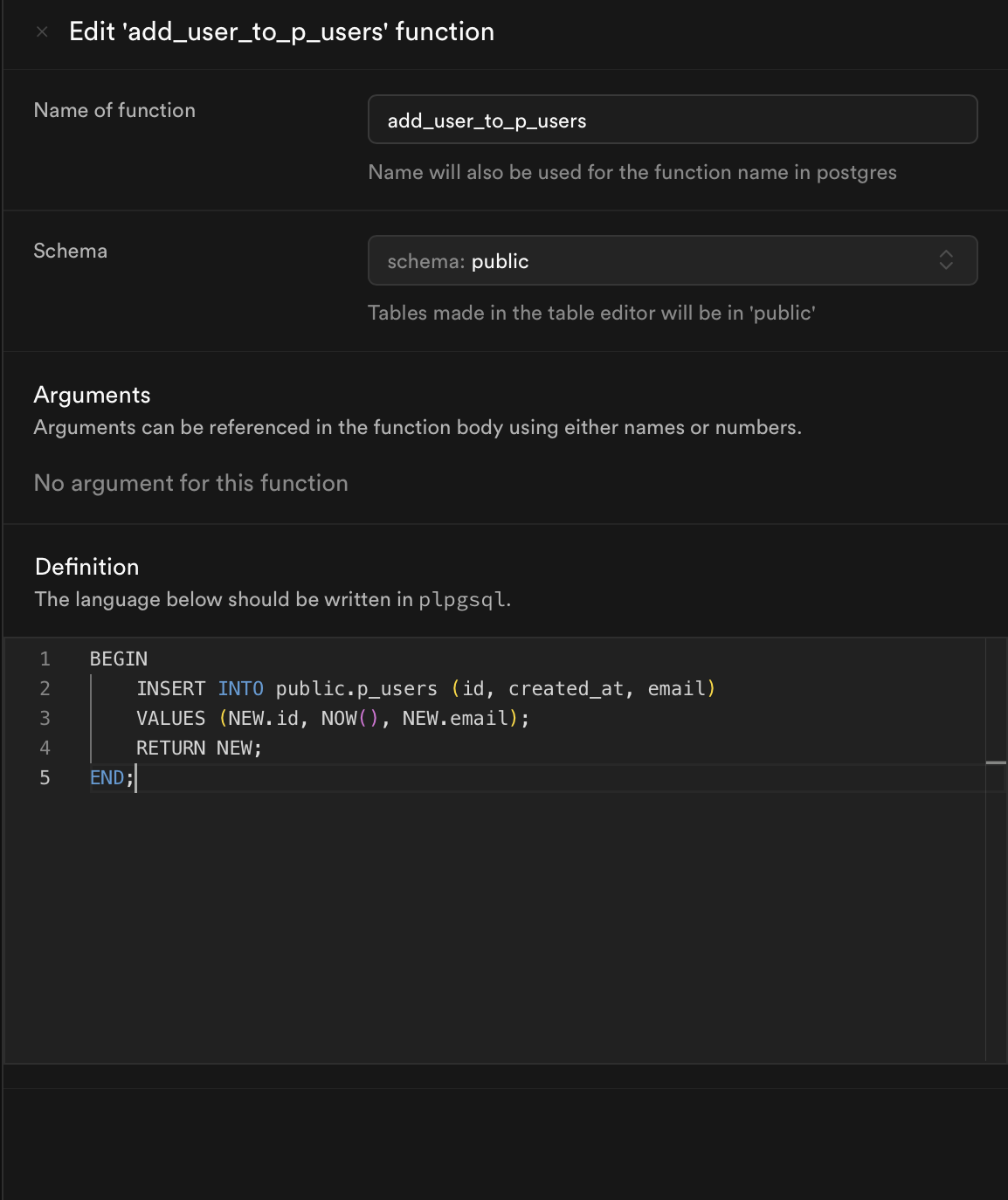
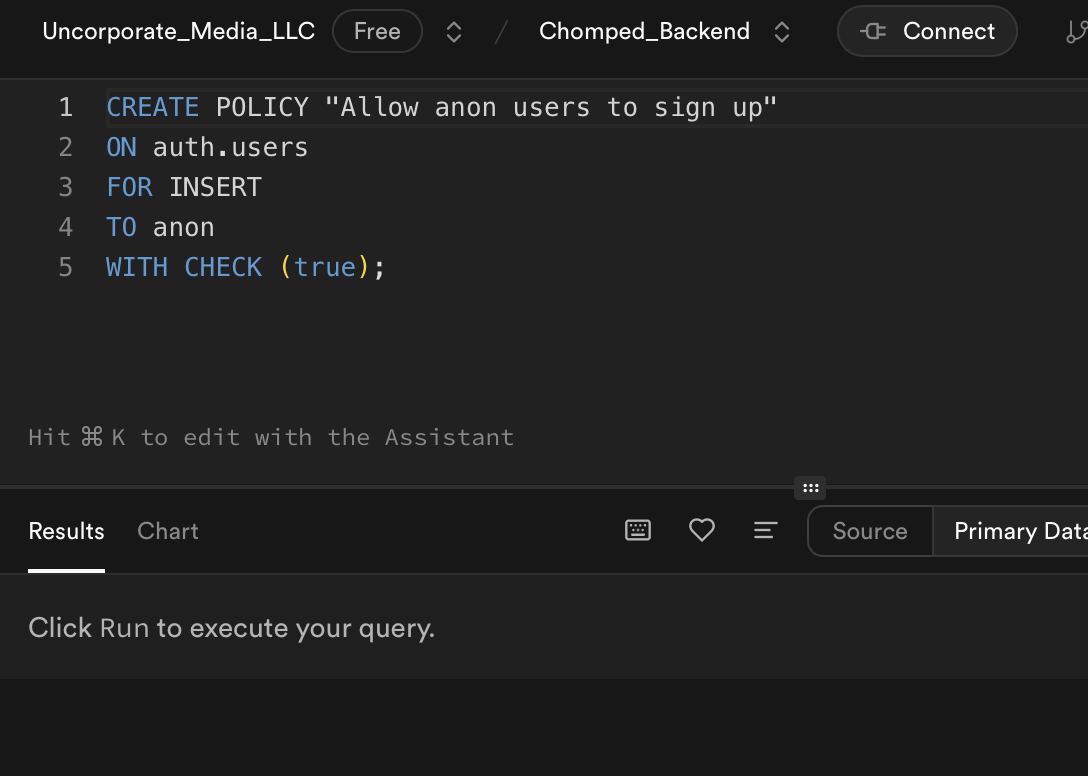
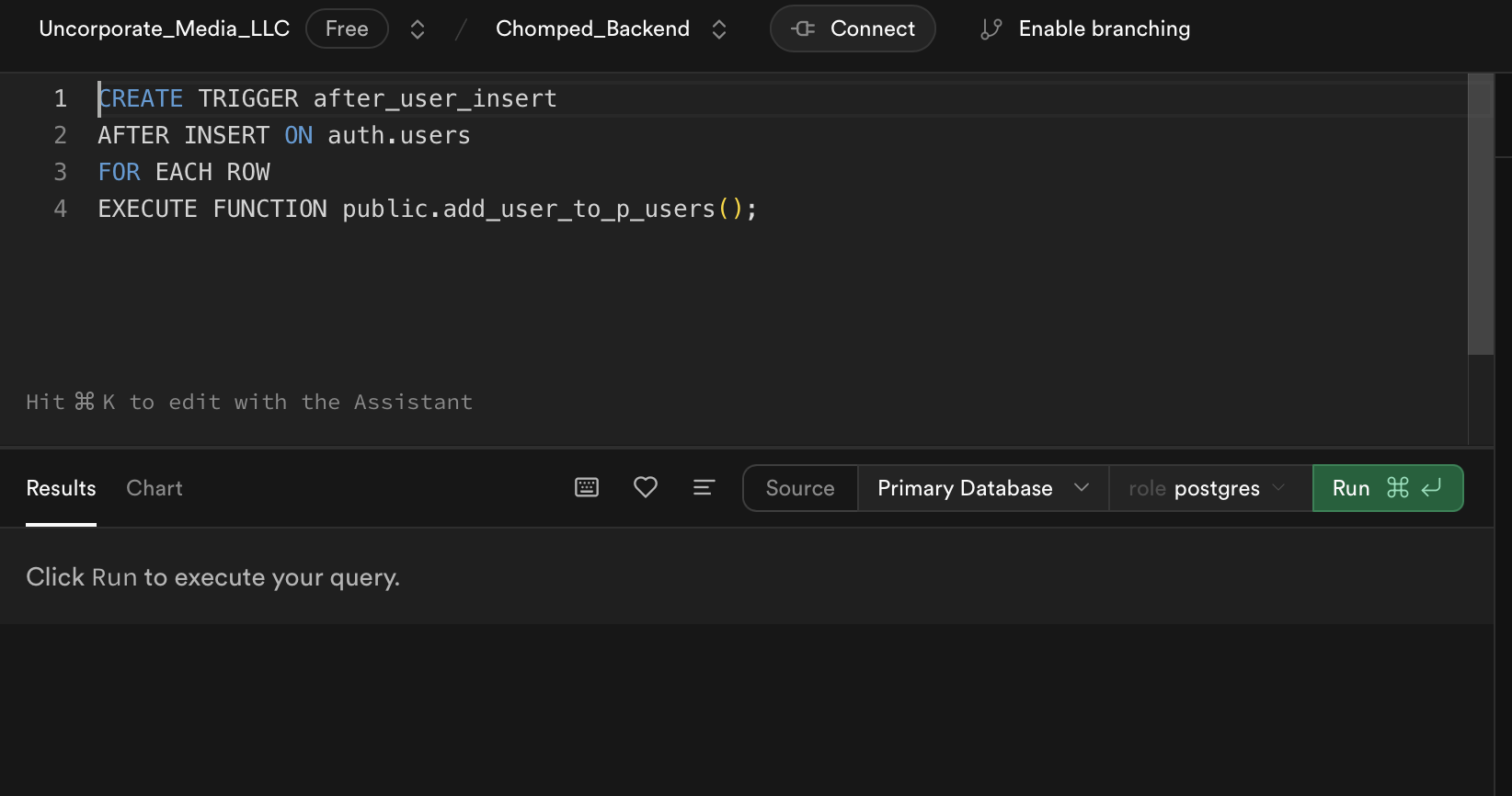
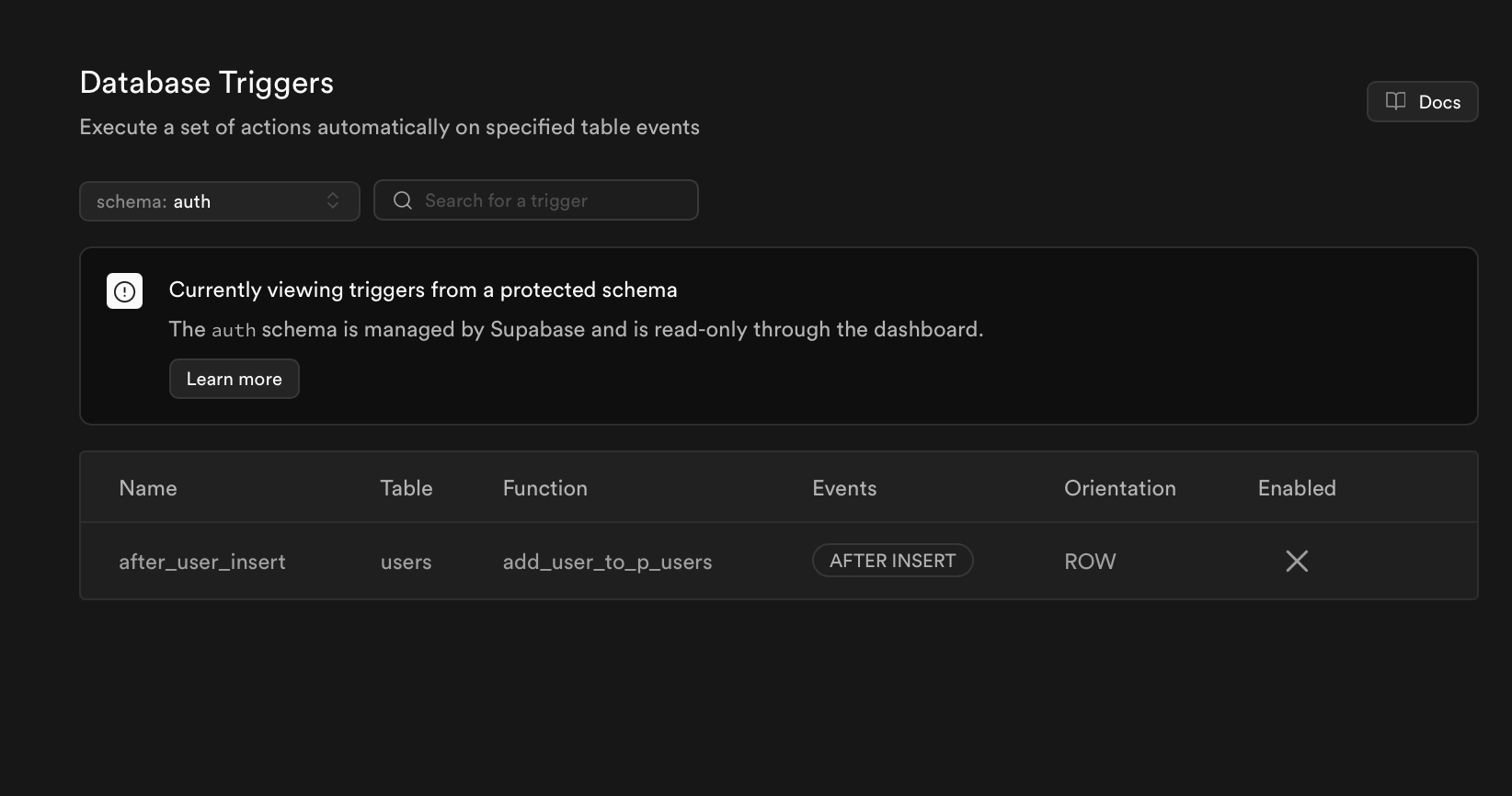
Below, I’ve included the simple function and trigger I’m using to handle this.
The Issue
-I’m using the anon key for the app, so the anon role is being used.
-When I manually insert rows into the auth.users table as the postgres role, everything works fine, and the data gets inserted into the p_users table via the trigger.
-However, when the app (under the anon role) inserts into auth.users, I get the following error:
ERROR: 42501: permission denied for table users
I tried creating a policy that allows the anon role to insert into the auth.users table, but it’s not working.
Additional Observations:
If I disable the trigger, the app can successfully insert into the auth.users table as the anon role, but no data gets copied into the p_users table (as expected without the trigger).
Error Logs
API Gateway Log:
POST | 500 | 96.56.181.14 | 900faace3bbf42a9 | https://pqnlwvndpizjspdplftc.supabase.co/auth/v1/signup | Chomped_App
Auth Log:
500: Database error saving new user
I’d appreciate any guidance on what I might be missing or need to fix to allow the trigger to work with the anon role. Thank you in advance for your help!
I'm new to Supabase and SQL, and while I'm slowly getting the hang of it, I've been stuck on this issue for days and could really use some help.
What I'm Trying to Solve
I’m building an iOS app and creating a login system. I want to take newly inserted information from the auth.users table (specifically, ID, email, and password) and copy it into a table in the public schema (p_users).
Below, I’ve included the simple function and trigger I’m using to handle this.
The Issue
-I’m using the anon key for the app, so the anon role is being used.
-When I manually insert rows into the auth.users table as the postgres role, everything works fine, and the data gets inserted into the p_users table via the trigger.
-However, when the app (under the anon role) inserts into auth.users, I get the following error:
ERROR: 42501: permission denied for table users
I tried creating a policy that allows the anon role to insert into the auth.users table, but it’s not working.
Additional Observations:
If I disable the trigger, the app can successfully insert into the auth.users table as the anon role, but no data gets copied into the p_users table (as expected without the trigger).
Error Logs
API Gateway Log:
POST | 500 | 96.56.181.14 | 900faace3bbf42a9 | https://pqnlwvndpizjspdplftc.supabase.co/auth/v1/signup | Chomped_App
Auth Log:
500: Database error saving new user
I’d appreciate any guidance on what I might be missing or need to fix to allow the trigger to work with the anon role. Thank you in advance for your help!