Injection of a banned IPv4
Hello,
We have more than 100,000 IPv4s in a list that we want to ban. At the moment I'm running a python script but it's very time-consuming. Is there any other way of injecting?
Script python made in chatgpt :
33 Replies
Important Information
Thank you for getting in touch with your support request. To expedite a swift resolution, could you kindly provide the following information? Rest assured, we will respond promptly, and we greatly appreciate your patience. While you wait, please check the links below to see if this issue has been previously addressed. If you have managed to resolve it, please use run the command
/resolve or press the green resolve button below.Log Files
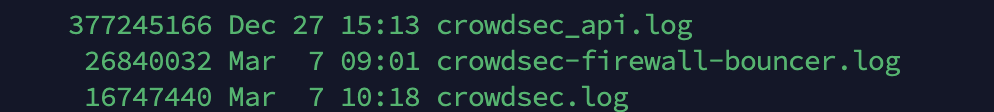
If you possess any log files that you believe could be beneficial, please include them at this time. By default, CrowdSec logs to /var/log/, where you will discover a corresponding log file for each component.
Guide Followed (CrowdSec Official)
If you have diligently followed one of our guides and hit a roadblock, please share the guide with us. This will help us assess if any adjustments are necessary to assist you further.
Screenshots
Please forward any screenshots depicting errors you encounter. Your visuals will provide us with a clear view of the issues you are facing.
© Created By WhyAydan for CrowdSec ❤️
So I wouldnt call
subpress.run with cscli decisions add as that would indeed take ages, instead you can pipe them in via stdin like
decisions import will do the batching and formatting for youif you want to see all flags and stuff https://docs.crowdsec.net/docs/next/cscli/cscli_decisions_import
cscli decisions import | CrowdSec
cscli decisions import
cause each
cscli decisions add is a http request, so you most likely DOS yourself if you not careful, import will send batches of lists of alerts so more optimisedOK, but I ‘m using crowdsec as a multiserv, can I filter that some machines can ’t receive alerts with the T-Pot-Detection reason ?
this will prevent the ipset of other machines from being shielded, because then I can forward the information to a router
You can if the remediation supports the flag to filter by scenario name then you can just add
T-Pot-Detection to either the allow or deny listOn the master server?
Well no it has to be done whereever your doing the remediation
or I have to do it on each machine
Which remediation are you using?
crowdsec-firewall-bouncer-iptables (debian/ubuntu) / (freebsd) crowdsec-firewall-bouncer
then you can use the https://docs.crowdsec.net/u/bouncers/firewall#scenarios_containing configurations to ignore scenarios, but this has to be done on each remediation as currently CrowdSec doesnt know which remediation it should or should not send these too
Firewall | CrowdSec
📚 Documentation
The problem is that it's not a scenario.
yes technically but the
--reason when used with import adds it as the scenario nameExemple :
scenarios_not_containing: ["T-Pot-Detection"]
Yes
Okay
Just to ask, is the remediation you wanting to update the ones hosting the T-Pots?
No, others vms
cscli alerts list
ERRO error while performing request: dial tcp 127.0.0.1:8081: i/o timeout; 4 retries left
INFO retrying in 22 seconds (attempt 2 of 5)
Aie aie Hello @iiamloz, I encounter an anomaly sometimes crowdsec-firewall explodes and authorises my scenarios which are ignored
Aie aie Hello @iiamloz, I encounter an anomaly sometimes crowdsec-firewall explodes and authorises my scenarios which are ignored
What do you mean by explodes ?
Does it crash ?
Do you see any errors in the logs ? (both for the bouncer and crowdsec itself)
It crashes and injects all ignored scenarios, so I have to restart crowdsec-firewall.
I'll send it tomorrow
Every day, he crashes
Mar 05 11:07:50 crowdsec-firewall-bouncer[1632053]: time="2025-03-05T11:07:50+01:00" level=fatal msg="process terminated with e>
Mar 05 11:07:50 systemd[1]: crowdsec-firewall-bouncer.service: Main process exited, code=exited, status=1/FAILURE
Mar 05 11:07:50 systemd[1]: crowdsec-firewall-bouncer.service: Failed with result 'exit-code'.
Mar 05 11:07:50 systemd[1]: Stopped The firewall bouncer for CrowdSec.
Mar 05 11:07:50 systemd[1]: Starting The firewall bouncer for CrowdSec...
Mar 05 11:07:56 systemd[1]: Started The firewall bouncer for CrowdSec.
Mar 06 14:00:35 systemd[1]: Stopping The firewall bouncer for CrowdSec...
Mar 06 14:00:37 crowdsec-firewall-bouncer[1689256]: time="2025-03-06T14:00:37+01:00" level=fatal msg="process terminated with e>
Mar 06 14:00:37 systemd[1]: crowdsec-firewall-bouncer.service: Main process exited, code=exited, status=1/FAILURE
Mar 06 14:00:37 systemd[1]: crowdsec-firewall-bouncer.service: Failed with result 'exit-code'.
Mar 06 14:00:37 systemd[1]: Stopped The firewall bouncer for CrowdSec.
Mar 06 14:00:37 systemd[1]: Starting The firewall bouncer for CrowdSec...
Mar 06 14:00:44 systemd[1]: Started The firewall bouncer for CrowdSec.
@blotusI have to restart
There should be additional logs in
/var/log/crowdsec-firewall-bouncer.log that would be useful alsotime="2025-03-06T13:10:56+01:00" level=error msg="auth-api: auth with api key failed return nil response, error: dial tcp xxx:8080: connect: connection refused"
time="2025-03-06T13:10:56+01:00" level=error msg="Get "http://x:8080/v1/decisions/stream?scenarios_not_containing=T-Pot-Detection\": dial tcp :8080: connect: connection refused"
time="2025-03-06T13:11:07+01:00" level=info msg="15000 decisions added"
time="2025-03-06T13:32:56+01:00" level=info msg="1 decision added"
time="2025-03-06T13:42:46+01:00" level=info msg="1 decision added"
time="2025-03-06T13:43:46+01:00" level=info msg="1 decision deleted"
time="2025-03-06T14:00:35+01:00" level=info msg="Shutting down backend"
time="2025-03-06T14:00:35+01:00" level=info msg="Deleting rule : /usr/sbin/iptables -D INPUT -j CROWDSEC_CHAIN"
time="2025-03-06T14:00:35+01:00" level=info msg="Flushing chain : /usr/sbin/iptables -F CROWDSEC_CHAIN"
time="2025-03-06T14:00:35+01:00" level=info msg="Deleting chain : /usr/sbin/iptables -X CROWDSEC_CHAIN"
time="2025-03-06T14:00:36+01:00" level=info msg="Deleting rule : /usr/sbin/ip6tables -D INPUT -j CROWDSEC_CHAIN"
time="2025-03-06T14:00:36+01:00" level=info msg="Flushing chain : /usr/sbin/ip6tables -F CROWDSEC_CHAIN"
time="2025-03-06T14:00:36+01:00" level=info msg="Deleting chain : /usr/sbin/ip6tables -X CROWDSEC_CHAIN"
time="2025-03-06T14:00:37+01:00" level=fatal msg="process terminated with error: received SIGTERM"
time="2025-03-06T14:00:37+01:00" level=info msg="Starting crowdsec-firewall-bouncer v0.0.31-debian-pragmatic-amd64-"
time="2025-03-06T14:00:37+01:00" level=info msg="backend type: iptables"
time="2025-03-06T14:00:37+01:00" level=info msg="using 'DROP' as deny_action"
time="2025-03-06T14:00:37+01:00" level=info msg="iptables for ipv4 initiated"
time="2025-03-06T14:00:37+01:00" level=info msg="Deleting rule : /usr/sbin/iptables -D INPUT -j CROWDSEC_CHAIN"
time="2025-03-06T14:00:37+01:00" level=error msg="error while removing rule : exit status 2 --> iptables v1.8.4 (legacy): Couldn't load target
CROWDSEC_CHAIN':No such file or directory\n\nTry iptables -h' or 'iptables --help' for more information.\n"
time="2025-03-06T14:00:38+01:00" level=info msg="Flushing chain : /usr/sbin/ip6tables -F CROWDSEC_CHAIN"
time="2025-03-06T14:00:38+01:00" level=error msg="error while flushing chain : exit status 1 --> ip6tables: No chain/target/match by that name.\n"
time="2025-03-06T14:00:38+01:00" level=info msg="Deleting chain : /usr/sbin/ip6tables -X CROWDSEC_CHAIN"
time="2025-03-06T14:00:38+01:00" level=error msg="error while deleting chain : exit status 1 --> ip6tables: No chain/target/match by that name.\n"
time="2025-03-06T14:00:39+01:00" level=info msg="Creating chain : /usr/sbin/ip6tables -N CROWDSEC_CHAIN -t filter"
time="2025-03-06T14:00:39+01:00" level=info msg="Adding rule : /usr/sbin/ip6tables -I INPUT -j CROWDSEC_CHAIN"
time="2025-03-06T14:00:39+01:00" level=info msg="Using API key auth"
time="2025-03-06T14:00:39+01:00" level=info msg="config is valid"
on another machine I have the same problem but it's at storage level, and it's a domino effecthmmm the only thing that is odd is the
time="2025-03-06T13:11:07+01:00" level=info msg="15000 decisions added" cause of the restrictions, could you check /var/log/crowdsec-api.log around those times to see what request that came inWtff It's been out of date since december but be careful, I'm on a multiserver system and I've disabled the api on systemctl.
Yes if you run multiserver apologies, I meant check the api log on the LAPI (I didnt know beforehand)
I have just checked my systemd and discovered that I had forgotten -no-api
on the main server I get logs like this
T-Pot-Detection by ip 31.184.198.71 : 72h ban on Ip 31.184.198.71"
but on the main LAPI server there should be the api logs?
yes I have
time="2025-03-06T13:11:59+01:00" level=info msg="(xxxxxx/cscli) T-Pot-Detection by ip 206.168.34.38 : 72h ban on Ip 206.168.34.38"
time="2025-03-06T13:11:59+01:00" level=info msg="(xxxxxx/cscli) T-Pot-Detection by ip 5.1.1.1 : 72h ban on Ip 5.1.1.1"
that should be in
crowdsec.log not crowdsec-api.log we want the latterOupsss
I didn't see it when I copied my .gz file
I'm waiting for the problem to return as I only have the 5pm logs.