A little randomly, Crowdsec's main website will not be reachable
My guess is, some component of the "https://app.crowdsec.net/" is not able to load, possibly the first/primary part and according to Chrome's DevTools, it is - nothing loads
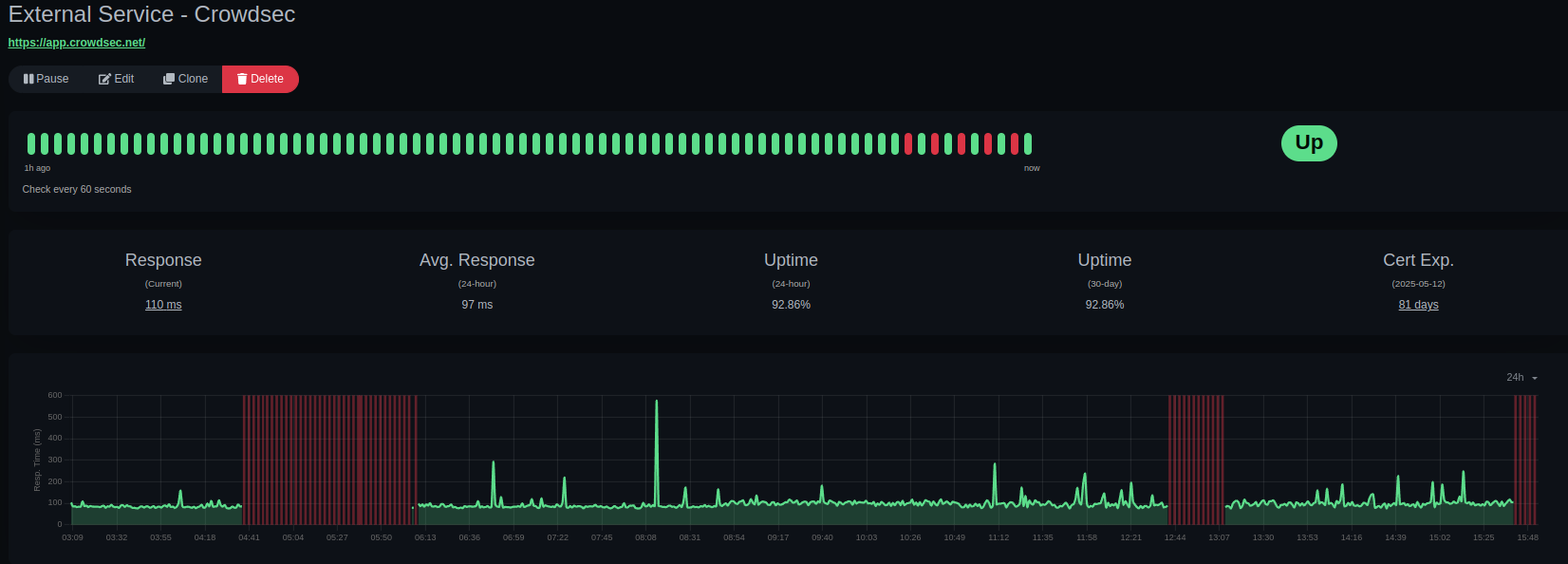
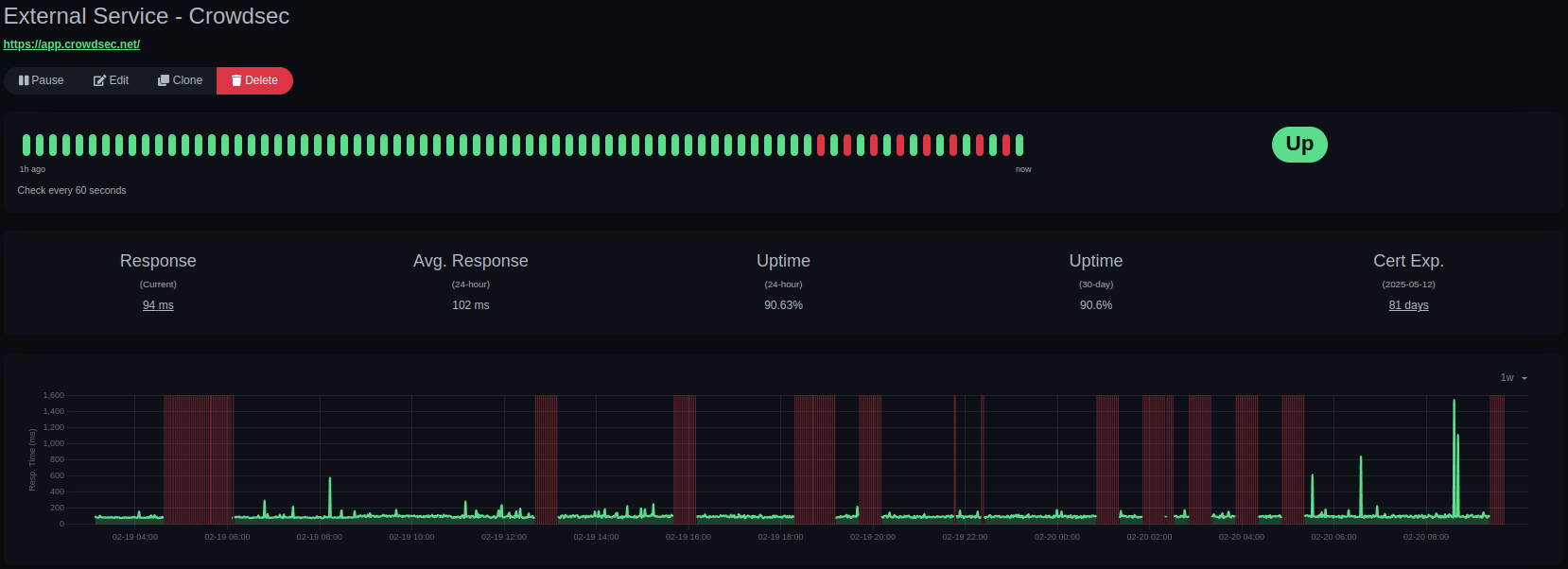
Attached a screenshot of my Uptime - Kuma for Crowdsec behind my OPNSense that is my Multi-site LAPI - this tracks for my Chrome browser too - if I switch on my phone to 5G, it loads no problem
Is there anything we would need to do to prevent CDN/Cloud/Crowdsec IPs from getting on our/your lists? This is my guess that it is Crowdsec blocking Crowdsec, but it might be my Pihole+Unbound config, but, AFAIK your primary domain has never found itself on the Adblock lists.
8 Replies
Important Information
Thank you for getting in touch with your support request. To expedite a swift resolution, could you kindly provide the following information? Rest assured, we will respond promptly, and we greatly appreciate your patience. While you wait, please check the links below to see if this issue has been previously addressed. If you have managed to resolve it, please use run the command
/resolve or press the green resolve button below.Log Files
If you possess any log files that you believe could be beneficial, please include them at this time. By default, CrowdSec logs to /var/log/, where you will discover a corresponding log file for each component.
Guide Followed (CrowdSec Official)
If you have diligently followed one of our guides and hit a roadblock, please share the guide with us. This will help us assess if any adjustments are necessary to assist you further.
Screenshots
Please forward any screenshots depicting errors you encounter. Your visuals will provide us with a clear view of the issues you are facing.
© Created By WhyAydan for CrowdSec ❤️
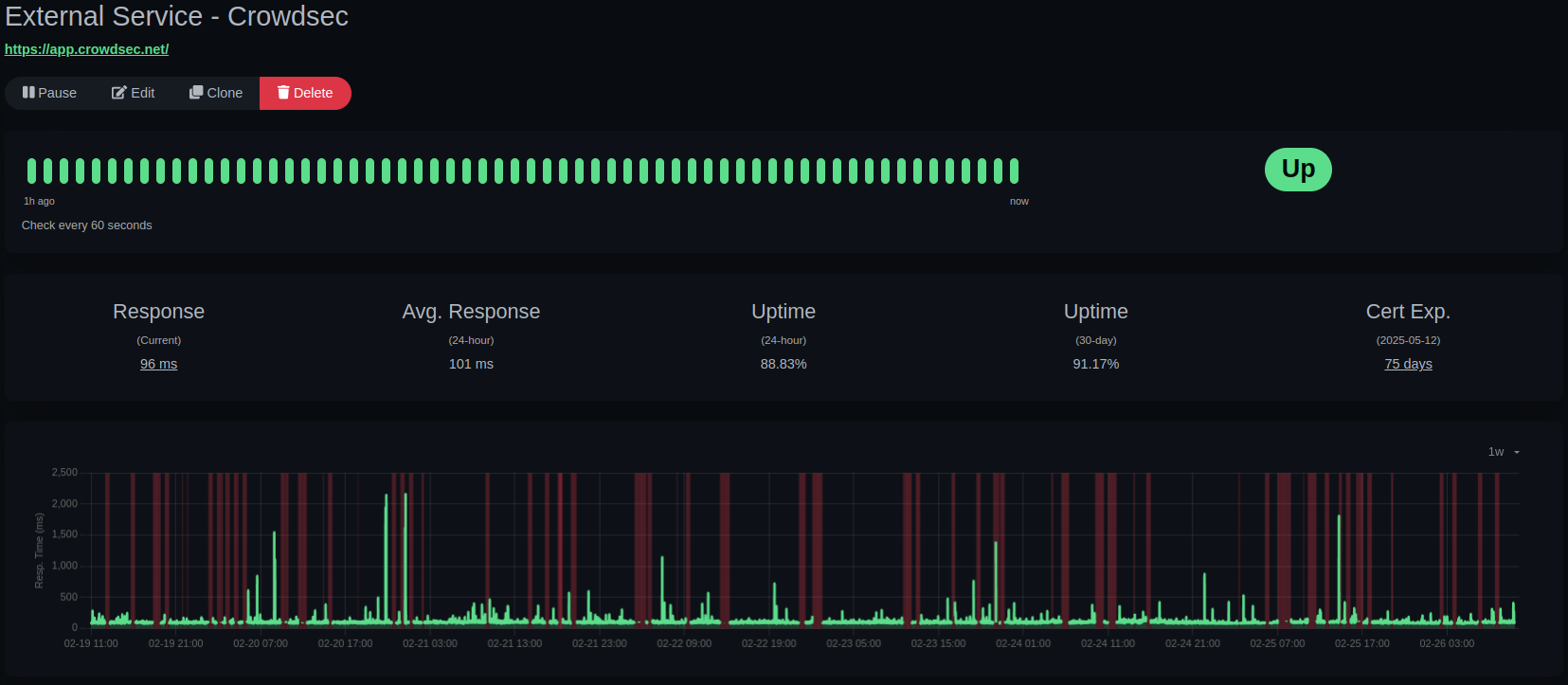
Truly is rather random...
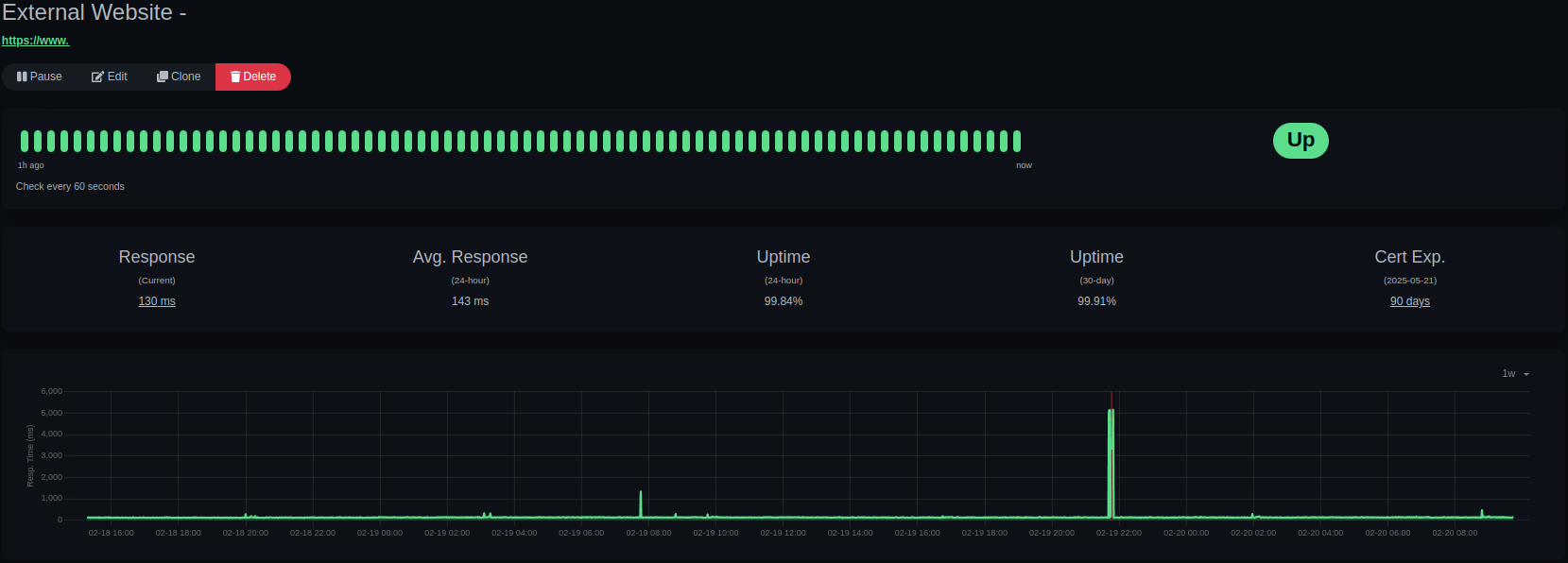
A different website I host at a VPS checked from the same env as the checks above ^
In short - just showing that my internet is working, this appears to be a response/availability issue for Crowdsec's Cloud Infra?
That's really weird, we haven't seen this kind of issue.
The check is only making a simple request, so you are just basically hitting Vercel infrastructure and it returns the (static) front code.
Maybe a weird issue between your ISP and vercel ?
Hmm, possibly but unlikely as the ISP is pretty big
Just wanted to see if you check the lists you send against your local+cloud infra IPs, and further, that the Crowdsec Parsers/etc. wouldn't attempt to block you (Crowdsec + Crowdsec-CDN/Cloud IPs), and to make sure we shouldn't have to keep our LAPI+parsers from blocking you?
Re: DNS level adblocking (unbound + pihole), is there any chance that we might have to allow some FQDN that you use for infra or even the crowdsec as an Adblock allowlist FQDN? what would those FQDNs be?
I have port forwarding + firewall rules setup for all (most? but likely all) DNS traffic if anything on my network attempts to "use someone else's DNS", it will redirect them back to my internal DNS, and so, VERY thorough adblocking
last but not least, how would you suggest I test the vercel infra from my connection, what FQDN/test type could I make for them to see if the issue happens as the same time?
So I've added the Vercel subnet to my capi-whitelists.yaml file, curious if there are any other subnets to add to ensure oddities to not persist, that said, the capi-whitelists.yaml file so far has not been the remedy
Additionally, it would be neat if the 'capi-whitelists.yaml' file could work as IPs/Subnets/FQDNs/ASNs because... generally you have a whole FQDN/ASN you won't want to block not just a Subnet and/or the FQDN or ASN won't change but the subnets could
i would have been very surprised if it had fixed the issue.
When you fail to query app.crowdsec.net, do you see any errors in your crowdsec logs ? (app.crowdsec.net is not used by crowdsec, it would maybe point to a larger issue)
regarding supporting FQDN/ASN in the CAPI whitelists: unfortunately, it's not possible (or at least, not easy to do): CAPI only sends the IPs to crowdsec, so if you were to add a whitelist based on an ASN or rdns, we woulc need to do local lookups, which would be extremely slow
I really don't see a way for crowdsec to block access to the console.
If you grep 76.76.21.98 and 66.33.60.194 in
/var/log/crowdsec.log/ do you see anything ?
Same thing in the output of cscli decisions list --allHeh, since I'm running CrowdSec LAPI in docker, no, I don't have a log to scrap - might have to finally get all those logs sent to the data lake...
Heard, sounds like I would want to test the API URL, so I've moved to just ping 'api.crowdsec.net' instead of trying to load the HTTPS for it and auth
The api URL doesn't seem to be a basic auth endpoint and really, if it pings, that's good for me for now
Thank you @blotus !!