Have a working Traefik, trying to enable CrowdSec Appsec feature, need help
The CrowdSec Appsec feature is running in the same bouncer that is reading the Traefik logs, it might be neat to have Appsec running in the main LAPI, but it seems this is not how you are best to configure it.
There are two Traefik environments:
1 - Natural Port Forwarded from OPNSense Router to DMZ "ep" Traefik container w/its own Redis/Crowdsec
2 - CloudFlare Tunneled to DMZ "cf" Traefik container w/its own Redis/Crowdsec
There is a CrowdSec LAPI environment in its own container w/its own Postgres
I'm doing MACVLAN and each device has a RFC1918 address on the network
When I enable the CrowdSec feature for site XYZ, the XYZ page no longer responds (this one being browseable by way of a CloudFlare Tunnel) but the ABC page on the same tunnel works. XYZ page does load locally for the "ep" Traefik environment, but not externally.
Looking for ways to trouble shoot the paths and to make sure I'm 'activating' the Appsec feature in the correctly place, the CrowdSec docker container that is parsing the Traefik logs. My installation is Multi-Server, with a main CrowdSec running LAPI w/Postgres DB, several CrowdSec log parsers, and a few Bouncers. This is my first time exploring the Appsec feature, and while I've read a bit, have a few things yet to fully understand.
Thank you for reading, please help!!
23 Replies
Important Information
Thank you for getting in touch with your support request. To expedite a swift resolution, could you kindly provide the following information? Rest assured, we will respond promptly, and we greatly appreciate your patience. While you wait, please check the links below to see if this issue has been previously addressed. If you have managed to resolve it, please use run the command
/resolve or press the green resolve button below.Log Files
If you possess any log files that you believe could be beneficial, please include them at this time. By default, CrowdSec logs to /var/log/, where you will discover a corresponding log file for each component.
Guide Followed (CrowdSec Official)
If you have diligently followed one of our guides and hit a roadblock, please share the guide with us. This will help us assess if any adjustments are necessary to assist you further.
Screenshots
Please forward any screenshots depicting errors you encounter. Your visuals will provide us with a clear view of the issues you are facing.
© Created By WhyAydan for CrowdSec ❤️
Here's the example of my Middleware.yml
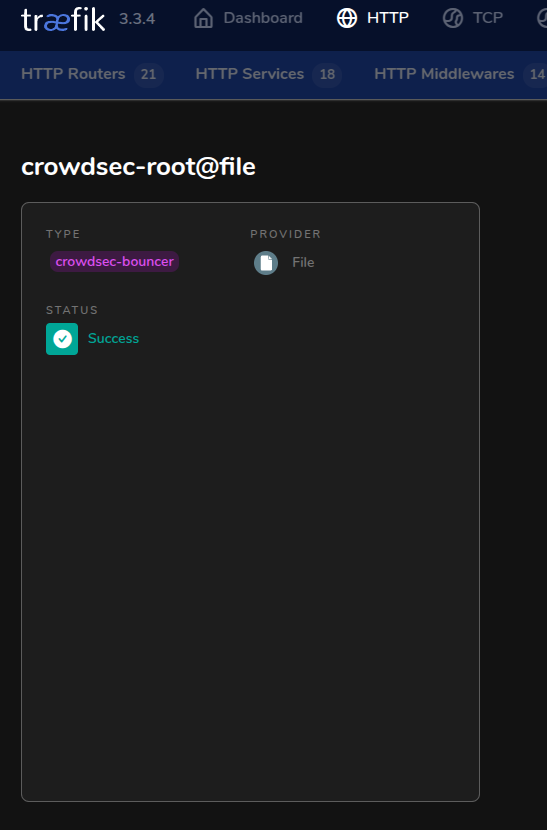
Here's the Middleware of CrowdSec showing up in Traefik
If you type
.env in your browser then you should see CrowdSec's blocked pageThat's one of my block commands... lol, if I see that requested in plain text it is added to the block list
Why is it there, and what does that mean?
It's a really common file used to store secrets, and way too many sysadmins have that file in webroot. It's meant to protect against that misconfiguration.
You are saying that if CrowdSec blocks a page, it puts something in .env that you can still browse to?
My issue is I get an eternal load, it never processes the request, or responds to the requestor
No, I'm saying if it finds
.env within the URL then it blocks the request from reaching the backend since it looks like it's trying to access an environment variable file.What I do not know yet, is how far the integration has processed it.. it would seem I don't see my Bouncer api-ed in, but I do see my log parser...
I'm testing it from outside on a 5G ip, it shouldn't (and as far as I know, doesn't the other sites without the CrowdSec Middlewares enable work) already be filtering me
if you get a CrowdSec block page when you visit
.env then that means AppSec is workingAhh, now I see, "how to trigger a block" I missed that, thank you, I'd like to be able to trigger a CrowdSec block, as of yet, if I enable it on a Route, that route only routes inside
The Traefik bouncer should be forwarding all requests to the Security Engine for inspection, if you want to whitelist a specific route then you'll have to write an AppSec rule to do that.
I only have Appsec-Default set
You don't have any of the vpatch rules installed, or the base config?
Is in the CrowdSec container for that Traefik
docker-compose.yml has this around that...
i also wrote a thing to cause it to hub update and hub upgrade as it seems to otherwise error on some files
getting that maxmind db, pretty cool
i also disable its server on the Traefik CrowdSec and have it configured to talk to the LAPI CrowdSec which is a different container in a different zone
the log parser signs in, but the bouncer never does
not sure, this is totally new space for me
I don't see https://app.crowdsec.net/hub/author/crowdsecurity/appsec-rules/base-config which isn't strictly necessary if you don't want to inspect the request body (If your using AppSec you'll want this anyway). Again, if you just visit your site protected by AppSec and visit
/.env then you should see a block page.
or you can just run this curl command: curl https://yourdomain.com/.env --head you should see 403 in the first line
Output should look something like this:
Adding to multiple docker-compose.yml - thank you
You just need to add it to the one docker container that has AppSec
Oh, I just checked out the https://app.crowdsec.net/hub/author/crowdsecurity/collections/appsec-generic-rules and it includes that already
in that case everything should work fine, just run the curl command I gave earlier and see if you get blocked.
for some reason, i cannot seem to use the redis cache, not sure why, but when i disabled the redis cache it has started working
@GNU Plus Windows User also, thank you for the ".env" test, that worked quiet well