auth.log seems to not get parsed
It seems my crowdsec instance is not parsing auth.log file from ubuntu linux.
I am running the crowdsec container, I have my auth.log mounted in the docker container.
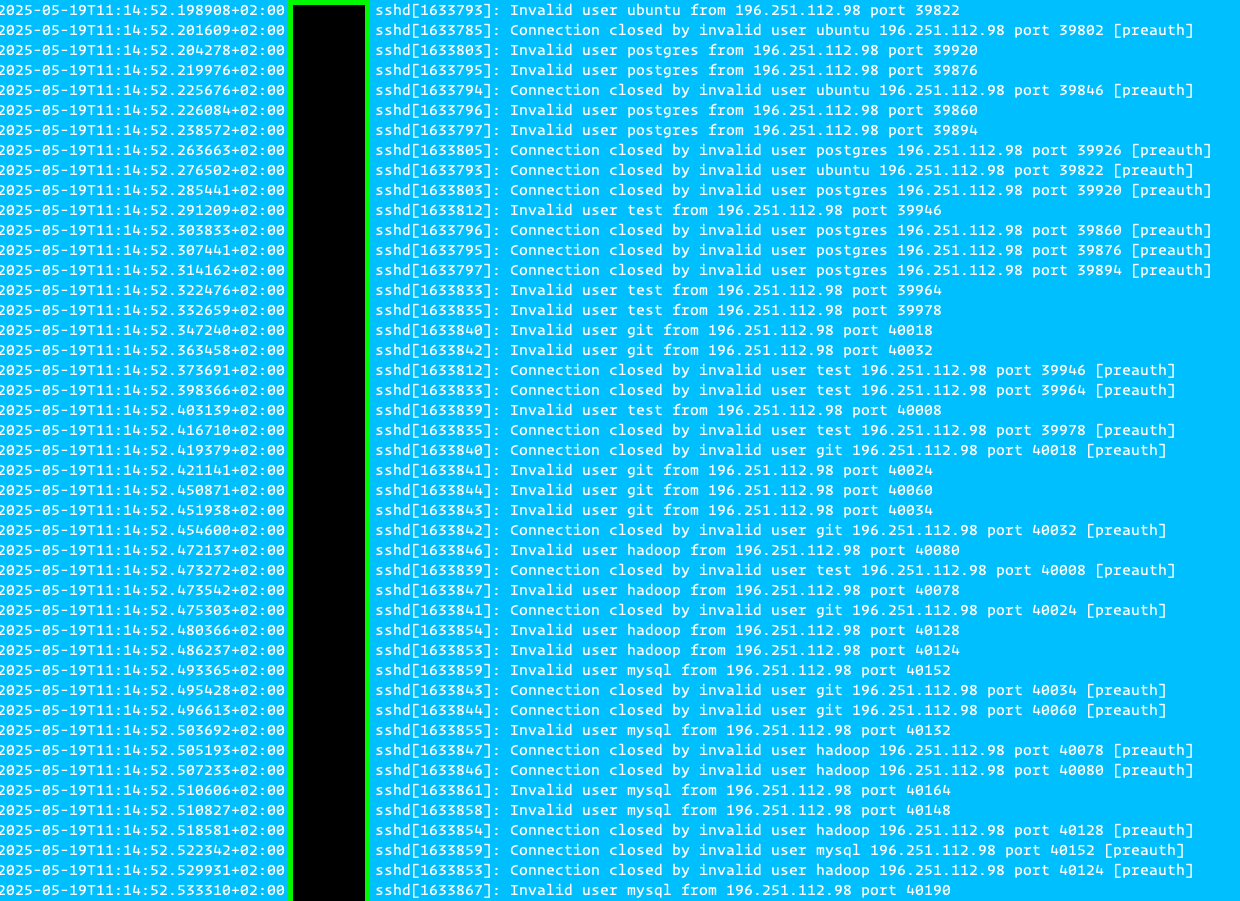
Here is the metrics output:
When I run on the auth.log cscli explain, it correctly detects scenarios:
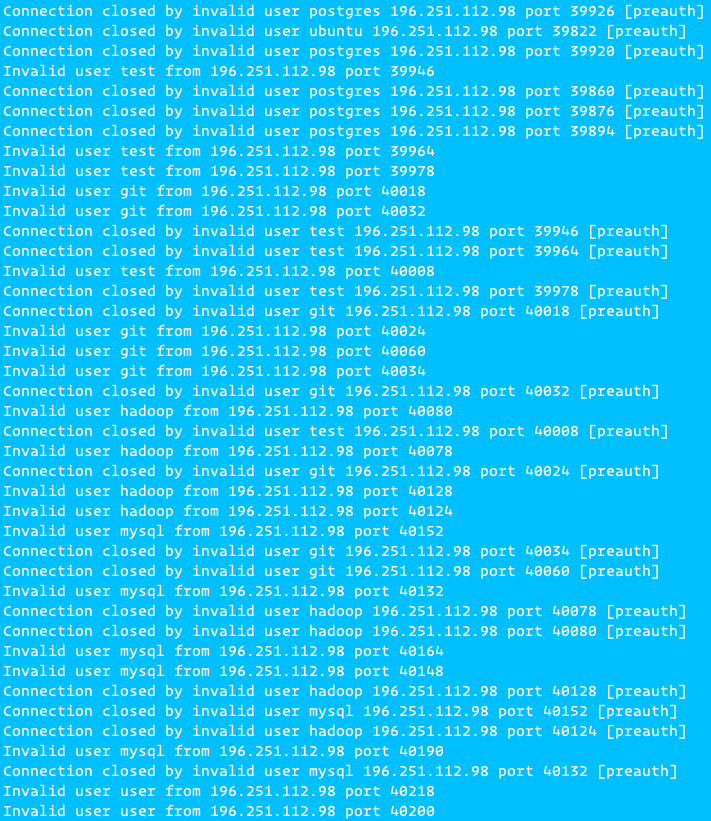
It also fails to parse some lines:
No decisions are made for the IPs that trigger scenarios.
I am running the crowdsec container, I have my auth.log mounted in the docker container.
Here is the metrics output:
When I run on the auth.log cscli explain, it correctly detects scenarios:
It also fails to parse some lines:
No decisions are made for the IPs that trigger scenarios.