Logs Not Being Parsed
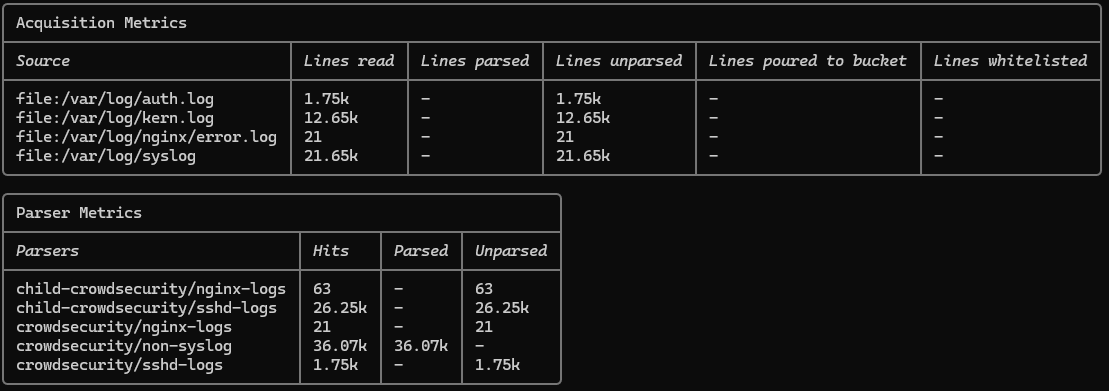
Hi - I'm running CrowdSec on my CloudPanel VPS (Ubuntu 24.04 LTS) and noticed that none of my logs are being parsed, even though lines are being read. Screenshots are attached for reference.
The CrowdSec engine and firewall bouncer are running fine.
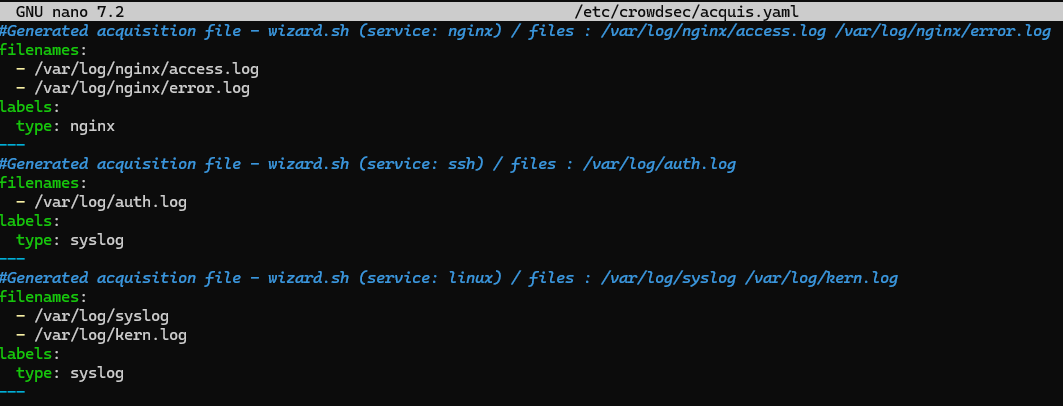
Following is the sample log format in /var/log/auth.log file:
2025-07-18T21:57:39.443985+05:00 MY-SERVER sudo: pam_unix(sudo:session): session opened for user root(uid=0) by USERNAME(uid=XXXX)
I am facing the same issue with all my VPSes. I need your help to resolve my problem. Thanks
The CrowdSec engine and firewall bouncer are running fine.
Following is the sample log format in /var/log/auth.log file:
2025-07-18T21:57:39.443985+05:00 MY-SERVER sudo: pam_unix(sudo:session): session opened for user root(uid=0) by USERNAME(uid=XXXX)
I am facing the same issue with all my VPSes. I need your help to resolve my problem. Thanks