Docker based log parser not connecting to Opnsense running LAPI
I am working on setting up crowdsec on my second network and im running into issues getting another machine connected to the LAPI running on opnsense.
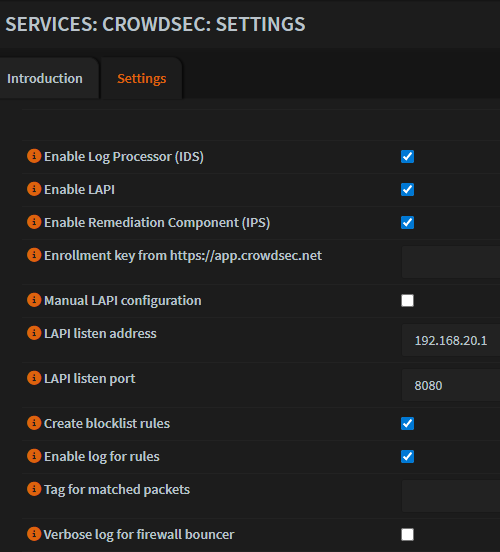
My opnsense crowdsec config can be see in the attached picture as well as the firewall rule on the LAN interface that allows the docker machine (an unraidbox) to connect to port 8080 on the router.
When running the
It is repeated over and over.
I have verified using curl that the docker server is able to connect to the opnsense box over 8080. There is also nothing being blocked in the opnsense firewall logs from either machine. Running
I played with this for a couple hours yesterday and Im at a loss of what to try next
My opnsense crowdsec config can be see in the attached picture as well as the firewall rule on the LAN interface that allows the docker machine (an unraidbox) to connect to port 8080 on the router.
When running the
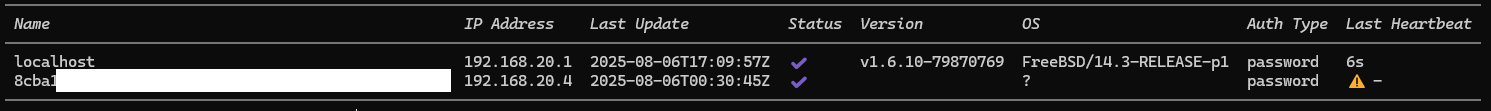
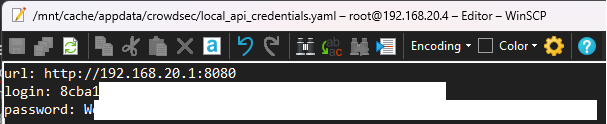
sudo cscli lapi register -u http://192.168.20.1:8080It is repeated over and over.
I have verified using curl that the docker server is able to connect to the opnsense box over 8080. There is also nothing being blocked in the opnsense firewall logs from either machine. Running
cscli machines listI played with this for a couple hours yesterday and Im at a loss of what to try next