Strungling with Bouncer Middleware in Traefik 3 on kubernetes.
Hy everyone, i wondering if someone allready have trouble to deploy bouncer middleware on traefik 3 ?
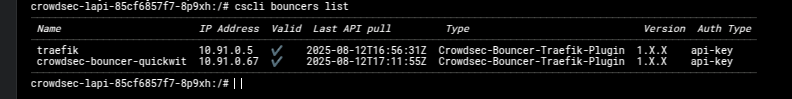
- Security engine is registered
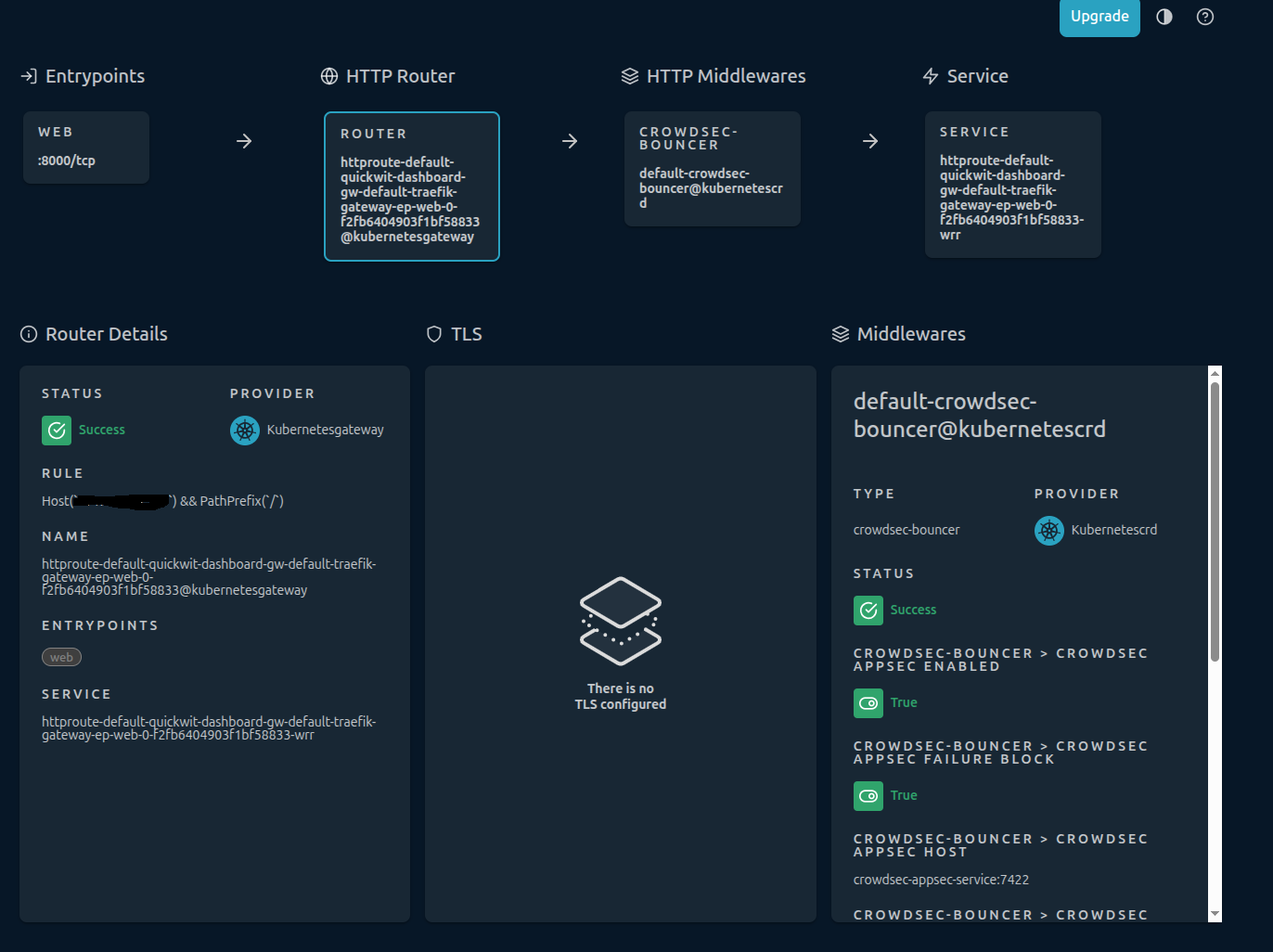
- traefik3 is deployed on kubenetes. Everything look ok but when i activate crowdsec middleware on HTTProute.
The subject is wide but it is upon activation of the middleware nothing will appear on console.
The plugin is however well installed, everything seems green on the traefik side.
6 Replies
Important Information
Thank you for getting in touch with your support request. To expedite a swift resolution, could you kindly provide the following information? Rest assured, we will respond promptly, and we greatly appreciate your patience. While you wait, please check the links below to see if this issue has been previously addressed. If you have managed to resolve it, please use run the command
/resolve or press the green resolve button below.Log Files
If you possess any log files that you believe could be beneficial, please include them at this time. By default, CrowdSec logs to /var/log/, where you will discover a corresponding log file for each component.
Guide Followed (CrowdSec Official)
If you have diligently followed one of our guides and hit a roadblock, please share the guide with us. This will help us assess if any adjustments are necessary to assist you further.
Screenshots
Please forward any screenshots depicting errors you encounter. Your visuals will provide us with a clear view of the issues you are facing.
© Created By WhyAydan for CrowdSec ❤️
Or traefik Helm value deployment:
Traefik refer that IngressRoute is mandatory for middleware but how to mix everything ? (ingressClass, KubernetesCRD and GatewayAPI). https://doc.traefik.io/traefik/reference/routing-configuration/kubernetes/gateway-api/#using-traefik-middleware-as-httproute-filter
We use CRD to define a namespaced middleware:
Gateway CRD to define a traefik's gatewayAPI:
And HTTProute to create the route:
Doest someone as a working setup like this ?
Traefik Kubernetes Gateway - Traefik
The Kubernetes Gateway API can be used as a provider for routing and load balancing in Traefik Proxy. View examples in the technical documentation.
Remediation component look empty
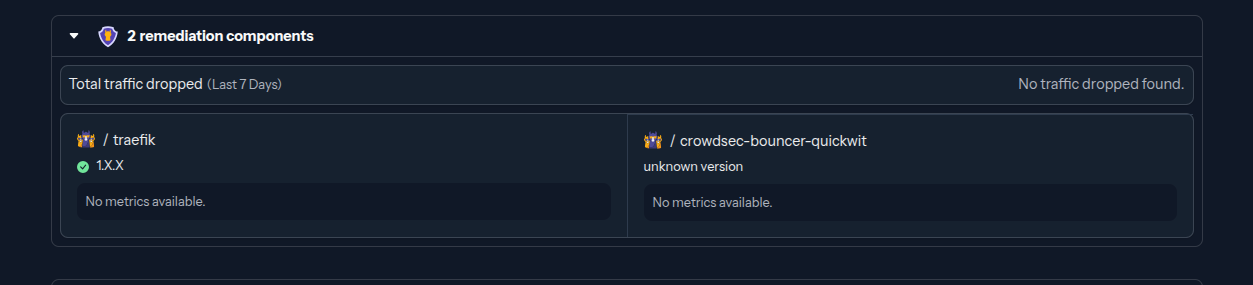
every bouncer are well registered and looks functionnal from local CLI